6.4 KiB
Logboek Security Infra
Notes
Change keyboard to us: sudo localectl set-keymap us
School DNS: 10.129.28.232,10.129.28.230
Fix cloudstack NM override
echo -e "network:\n config: disabled" | sudo tee /etc/cloud/cloud.cfg.d/06-netconfig-disabled.cfg > /dev/null
sudo nmcli connection modify "System enp3s0" ipv4.addresses 172.22.63.1/24
sudo nmcli connection modify "System enp3s0" ipv4.gateway 172.22.63.254
sudo nmcli connection modify "System enp3s0" ipv4.dns "10.129.28.232 10.129.28.230"
sudo nmcli connection modify "System enp3s0" ipv4.method manual
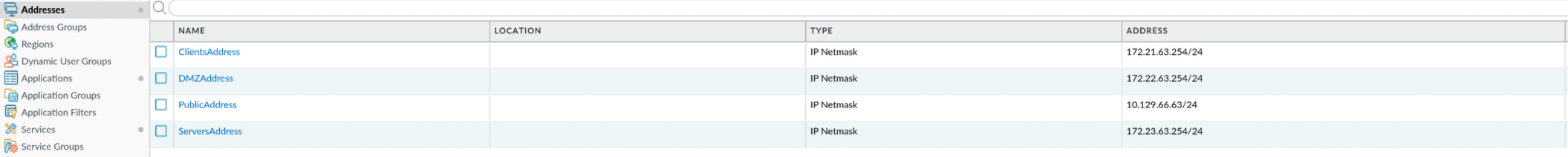
VM's
internal-servers:
RADIUS: 172.23.63.1 DHCP: 172.23.63.2
PKI: 172.23.63.4
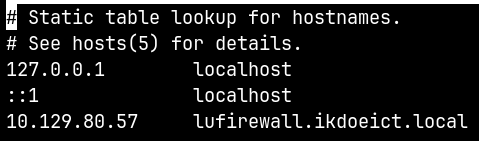
Firewall
management ip: 10.129.80.57 user: student ww: konijnkonijn
BasisConfiguratie
Management Interface: 1/0
Extras
Vertrouwde toegang tot de webinterface
sudo cp ca.crt /usr/share/ca-certificates/trust-source/anchors/si.crt
sudo update-ca-trust extract
Internte Auth ser
test authentication authentication-profile Admin-RADIUS username laszlo.uyttersprot password
Checkpoint
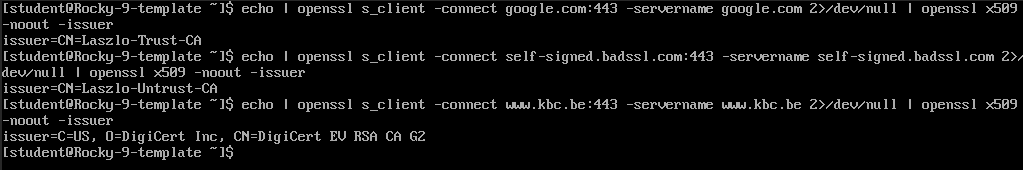
Decryption
Checkpoint
echo | openssl s_client -connect google.com:443 -servername google.com 2>/dev/null | openssl x509 -noout -issuer
echo | openssl s_client -connect self-signed.badssl.com:443 -servername self-signed.badssl.com 2>/dev/null | openssl x509 -noout -issuer
echo | openssl s_client -connect www.kbc.be:443 -servername www.kbc.be 2>/dev/null | openssl x509 -noout -issuer
Extra's
PKI
Setup
mkdir /pki
mkdir /pki/root
mkdir /pki/issuing
mkdir /pki/certs
RootCA
cd /pki/root
openssl genrsa -out RootCA_Key.pem 4096
openssl req -x509 -new -nodes -key RootCA_Key.pem \
-sha256 -days 3650 -out RootCA.pem \
-subj "/CN=Laszlo-Root-CA"
cd /pki/root
openssl genrsa -out UntrustCA_Key.pem 4096
openssl req -x509 -new -nodes -key UntrustCA_Key.pem \
-sha256 -days 3650 -out UntrustCA.pem \
-subj "/CN=Laszlo-Untrust-CA"
TrustCA
cd /pki/issuing
openssl genrsa -out TrustCA_Key.pem 4096
openssl req -new -key TrustCA_Key.pem -out TrustCA_CSR.pem \
-subj "/CN=Laszlo-Trust-CA"
openssl x509 -req -in TrustCA_CSR.pem \
-CA /pki/root/RootCA.pem -CAkey /pki/root/RootCA_Key.pem -CAcreateserial \
-out TrustCA.pem -days 3650 -sha256 \
-extfile <(printf "basicConstraints=CA:TRUE\nkeyUsage = keyCertSign, cRLSign")
rm -rf TrustCA_CSR.pem
AdminCA
cd /pki/issuing
openssl genrsa -out AdminCA_Key.pem 4096
openssl req -new -key AdminCA_Key.pem -out AdminCA_CSR.pem \
-subj "/CN=Laszlo-Admin-CA"
openssl x509 -req -in AdminCA_CSR.pem \
-CA /pki/root/RootCA.pem -CAkey /pki/root/RootCA_Key.pem -CAcreateserial \
-out AdminCA.pem -days 3650 -sha256 \
-extfile <(printf "basicConstraints=CA:TRUE\nkeyUsage = keyCertSign, cRLSign")
rm -rf AdminCA_CSR.pem
ManagementCert
cd /pki/certs
openssl genrsa -out Management_Key.pem 2048
openssl req -new -key Management_Key.pem -out Management_CSR.pem -subj "/CN=lufirewall.ikdoeict.local"
openssl x509 -req -in Management_CSR.pem \
-CA /pki/issuing/TrustCA.pem -CAkey /pki/issuing/TrustCA_Key.pem -CAcreateserial \
-out Management.pem -days 365 -sha256 \
-extfile <(printf "[SAN]\nsubjectAltName=DNS:lufirewall.ikdoeict.local") \
-extensions SAN
rm -rf Management_CSR.pem
cat Management.pem /pki/issuing/TrustCA.pem > Management_Fullchain.pem
OverrideCert
cd /pki/certs
openssl genrsa -out Override_Key.pem 2048
openssl req -new -key Override_Key.pem -out Override_CSR.pem -subj "/CN=172.21.63.254"
openssl x509 -req -in Override_CSR.pem \
-CA /pki/issuing/TrustCA.pem -CAkey /pki/issuing/TrustCA_Key.pem -CAcreateserial \
-out Override.pem -days 365 -sha256 \
-extfile <(printf "[SAN]\nsubjectAltName=IP:172.21.63.254") \
-extensions SAN
rm -rf Override_CSR.pem
cat Override.pem /pki/issuing/TrustCA.pem > Override_Fullchain.pem
student2Cert
cd /pki/certs
openssl genrsa -out student2_Key.pem 2048
openssl req -new -key student2_Key.pem -out student2_CSR.pem -subj "/CN=student2"
openssl x509 -req -in student2_CSR.pem \
-CA /pki/issuing/AdminCA.pem -CAkey /pki/issuing/AdminCA_Key.pem -CAcreateserial \
-out student2.pem -days 365 -sha256 \
-extfile <(echo "extendedKeyUsage=clientAuth")
rm -rf student2_CSR.pem
openssl pkcs12 -export -out student2.p12 -inkey student2_Key.pem -in student2.pem -certfile <(cat /pki/issuing/AdminCA.pem /pki/root/RootCA.pem) -name "student2"
GlobalProtectCert
cd /pki/certs
openssl genrsa -out GlobalProtect_Key.pem 2048
openssl req -new -key GlobalProtect_Key.pem -out GlobalProtect_CSR.pem -subj "/CN=globalprotect.ikdoeict.local"
openssl x509 -req -in GlobalProtect_CSR.pem \
-CA /pki/issuing/TrustCA.pem -CAkey /pki/issuing/TrustCA_Key.pem -CAcreateserial \
-out GlobalProtect.pem -days 365 -sha256 \
-extfile <(printf "[SAN]\nsubjectAltName=DNS:globalprotect.ikdoeict.local") \
-extensions SAN
rm -rf GlobalProtect_CSR.pem
UyttersprotCert
cd /pki/certs
openssl genrsa -out Uyttersprot_Key.pem 2048
openssl req -new -key Uyttersprot_Key.pem -out Uyttersprot_CSR.pem -subj "/CN=uyttersprot.si"
openssl x509 -req -in Uyttersprot_CSR.pem \
-CA /pki/issuing/TrustCA.pem -CAkey /pki/issuing/TrustCA_Key.pem -CAcreateserial \
-out Uyttersprot.pem -days 365 -sha256 \
-extfile <(printf "[SAN]\nsubjectAltName=DNS:uyttersprot.si") \
-extensions SAN
rm -rf Uyttersprot_CSR.pem
cat Uyttersprot.pem /pki/issuing/TrustCA.pem > Uyttersprot_Fullchain.pem
troubleshooting
full chanin in cert -> no fix cert zelf toevoegen aan paloalto -> no fix
openssl x509 -in student2.p12 -noout -text | grep -A1 "Authority Key Identifier"
openssl x509 -in AdminCA.pem -noout -text | grep -A1 "Subject Key Identifier"
Extra's verdediging
remote access (7%)
ssh
DMZ: 10.129.66.64:2201 EDL: 10.129.66.64:2202
Security Policies:
- Allow External SSH
NAT Policies:
- ssh DMZ
- ssh EDL
DNS server (7%)
uyttersprot.si
Security Policies:
- Allow DNS from Internal
- Allow DNS from untrust
- AppFilterLaszloUyttersprot1 (DNS weggehaalt)
NAT Policies:
- dns DMZ
DNSsec (7%)
dig @127.0.0.1 uyttersprot.si +dnssec
toon flasgs: ad toon RRSIG record
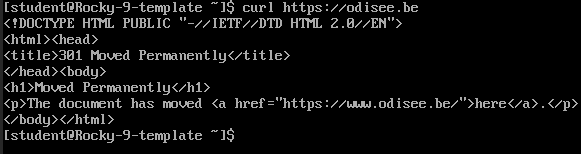
HTTPS (10%)
Incognito openen
http://uyttersprot.si -> werkt https://uyttersprot.si -> werkt en hsts is nu aan http://uyttersprot.si -> redirect